|
Code Virtualizer is a powerful code obfuscation system for Windows
applications that helps developers to protect their sensitive code areas
against Reverse Engineering with very strong obfuscation code, based on code
virtualization.
Code Virtualizer will convert your original code (Intel x86/x64
instructions) into Virtual Opcodes that will only be understood by an
internal Virtual Machine. Those Virtual Opcodes and the Virtual Machine
itself are unique for every protected application, avoiding a general attack
over Code Virtualizer.
Code Virtualizer can protect your sensitive code areas in any x32 and
x64 native PE/ELF/Mach-O files (like executable files/EXEs, system services,
DLLs , OCXs , ActiveX controls, shared objects, screen savers and device
drivers).
Basics about Reverse Engineering
When an application is being created, the Compiler will compile the
application source code into several object files made of machine language
code. Afterward, the object files are linked together to create the final executable.
 Figure 1: Compilation of your source code Figure 1: Compilation of your source code
When an attacker tries to crack a compiled application, he will use a
decompiler tool which will decompile the machine language code into a more
comprehensive code (like assembly code or a higher programming language),
doing his research over the decompiled code.
Figure 2: Decompilation of your application
When the attacker has a good knowledge of the target application, he can
modify the compiled application to alter its behavior. For example, the attacker
could bypass the routine that checks for the trial period in an application
and make it run forever, or, even worse, cause the application to behave as
if it was registered.
Code Virtualization against Reverse Engineering
Code virtualization consists of the transformation of binary code from a
specific machine into a different binary code that is understood by another
machine. That is, the instruction set from a specific machine is converted
into a new instruction set which is understood by a different machine. The
following picture represents the transformation from a block of Intel x86
instructions into a new instruction set for another machine (specifically a
RISC 32-bit CPU):
Figure 3: Transformation from x86 to RISC 32-bit CPU
Code Virtualizer can generate multiple types of virtual machines with a
different instruction set for each one. This means that a specific block of
Intel x86 instructions can be converted into different instruction set for
each machine, preventing an attacker from recognizing any generated virtual
opcode after the transformation from x86 instructions. The following picture
represents how a block of Intel x86 instructions is converted into different
kinds of virtual opcodes, which could be emulated by different virtual machines.
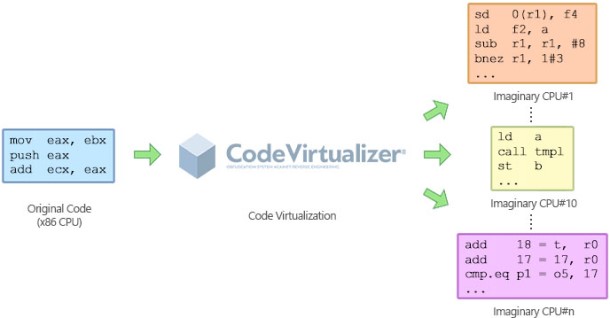
Figure 4: Transformation from x86 to multiple Imaginary CPUs
When an attacker tries to decompile a block of code that was protected
by Code Virtualizer, he will not find the original x86 instructions. Instead,
he will find a completely new instruction set which is not recognized by him
or any other special decompiler. This will force the attacker to go through
the extremely hard work of identifying how each opcode is executed and how
the specific virtual machine works for each protected application. Code
Virtualizer totally obfuscates the execution of the virtual opcodes and the
study of each unique virtual machine in order to prevent someone from
studying how the virtual opcodes are executed.
Code Virtualization in Real Life
Code Virtualizer can be embedded inside your Win32 and Win64
applications and device drivers with ease. You just need to select which
areas in your source code are going to be protected by Code Virtualizer. The
following example shows how you can protect a block of code in a C
application.
#include <stdio.h>
#include
"VirtualizerSDK.h"
void main()
{
VIRTUALIZER_START // the area to protect starts here
printf("Hello
World");
VIRTUALIZER_END // end of area to protect
}
The VIRTUALIZER_START/VIRTUALIZER_END macros are dummy macros which do
not interfere with the execution of the original application. It's only in
protection-time when Code Virtualizer will recognize those areas of code and
will covert them into unique virtual opcodes, which are then emulated by a
virtual machine when the protected application is running.
The following picture represents the image of an original compiled
application (before being protected) and how it's transformed when it's
protected by Code Virtualizer:
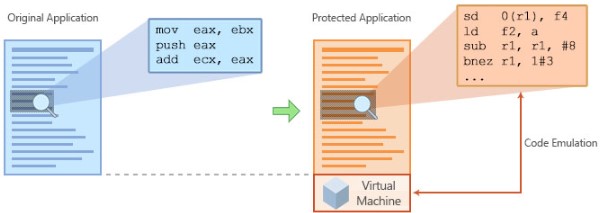 Figure 5: Original Application versus Protected Application
As the image shows, Code Virtualizer needs to embed the generated
virtual machine at the end of the protected application in order to emulate
the virtual opcodes when they are going to be executed.
Final Words
Code Virtualizer is a powerful technology that can prevent someone from
inspecting your sensitive code, such as your routines that validate an
entered serial key for registering your application. Also, Code Virtualizer
slightly modifies the header of the protected application, meaning you could
put a compressor or other software protector on top of Code Virtualizer with
no problems.
If you are a Windows device driver developer and felt neglected when
there was no solution to protect your device drivers, Code Virtualizer offers
you the same technology to do so (for either 32-bit and 64-bit drivers) in
the same way as your applications and DLLs.
Try Code Virtualizer today and start inserting the latest software
protection into your applications and device drivers!
Features
These are the key features of Code Virtualizer®:
- Obfuscation through multiples Virtual Machines
- Unique protection for every protected application
- Protection of any x32 and x64 application and Device Driver
- Advanced mutation engine
- Code relocation to protect DLLs and Device Drivers
- Emulation of any Intel x86 opcode inside unique Virtual Machines
- Unique virtual opcodes for every protected application
- Full compatible with any compressor/protector
- Command line protection
- and much more!
|

